Sony's PS3 Security is Epic Fail
The first few minutes of the conference were spent explaining the state of security on other consoles (Wii, 360, etc). Following this, the group went on to explain the current state of affairs on the PS3. First, explaining Geohot's memory line glitching exploit from earlier this year. The team then went on to explain the current PS3 security bypasses, such as jailbreaking and service mode/downgrading.
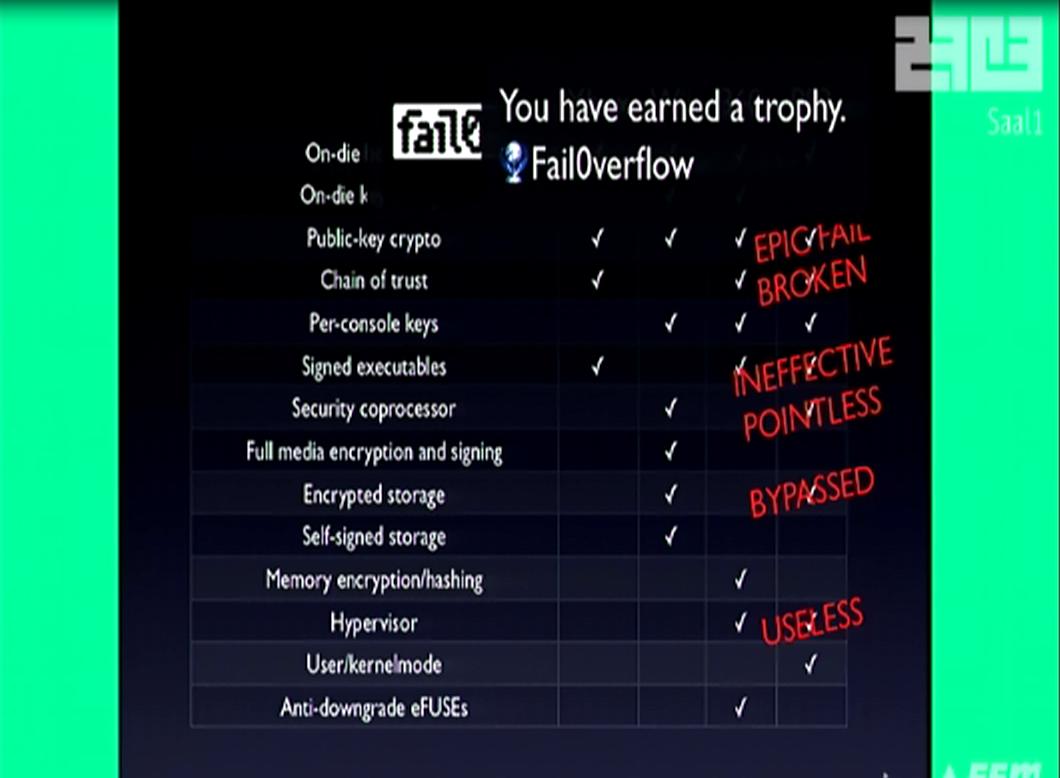
Approximately a half hour in, the team revealed their new PS3 secrets, the moment we all were waiting for. One of the major highlights here was, dongle-less jailbreaking by overflowing the bootup NOR flash, giving complete control over the system. The other major feat, was calculating the public private keys (due to botched security), giving users the ability to sign their own SELFs Following this, the team declared Sony's security to be EPIC FAIL!
The recent advent of these new exploits means current firmware is vulnerable, v3.55 and possibly beyond. It will be very difficult for Sony to fix the described exploits.
The team then displayed the website
http://fail0verflow.com/ were we assume will host examples of the new exploits and further details. They stated that easy to use tools would be coming next month.
Read more: PSGroove.com - Sony's PS3 Security is Epic Fail
http://psgroove.com/content.php?581-Sony-s-PS3-Security-is-Epic-Fail#ixzz19WMUJZAE